Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

Discover the role of a Chief Technology Officer in driving innovation and shaping tech strategy. Learn how CTOs lead digital transformation and engineering excellence.
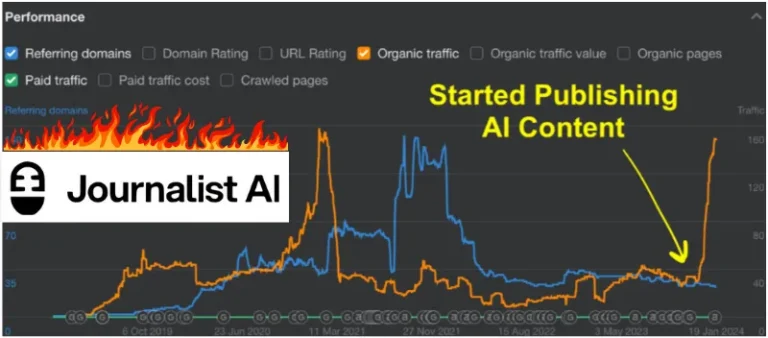
Discover how AI is revolutionizing journalism and blog writing. Our Journalist AI Review explores cutting-edge tools that enhance content creation and streamline workflows.

In a significant move to address the cybersecurity talent shortage, the White House has launched the “Service for America” program. This initiative aims to fill approximately 500,000 open cybersecurity positions across the United States by connecting Americans with jobs in…

India is set to bolster its cybersecurity defenses by training 5,000 cyber commandos over the next five years. This initiative, announced by Union Home Minister Amit Shah, aims to address the growing cyber threats and ensure national security in the…

Microsoft held a significant cybersecurity summit on Tuesday at its headquarters in Redmond, Washington, to address the vulnerabilities exposed by a global IT outage in July. The outage, caused by a faulty software update from CrowdStrike, affected nearly 8.5 million…

Discover the critical role of a Chief Information Security Officer in safeguarding your organization's digital assets and leading cybersecurity strategies for robust protection.

Discover the pivotal role of the CIO in driving digital transformation and strategic IT leadership. Learn how CIOs shape modern business success through technology.

Discover the essential roles and responsibilities of a CTO in tech leadership. Learn how CTOs drive innovation and shape IT strategy in modern organizations.

Unlock exclusive NordVPN coupons and save big on your online security. Discover the best deals and discounts for top-rated VPN protection. Get your nord vpn coupon today!

Discover the critical role of CISOs in safeguarding organizations. Learn about their responsibilities, challenges, and impact on cybersecurity strategy and risk management.